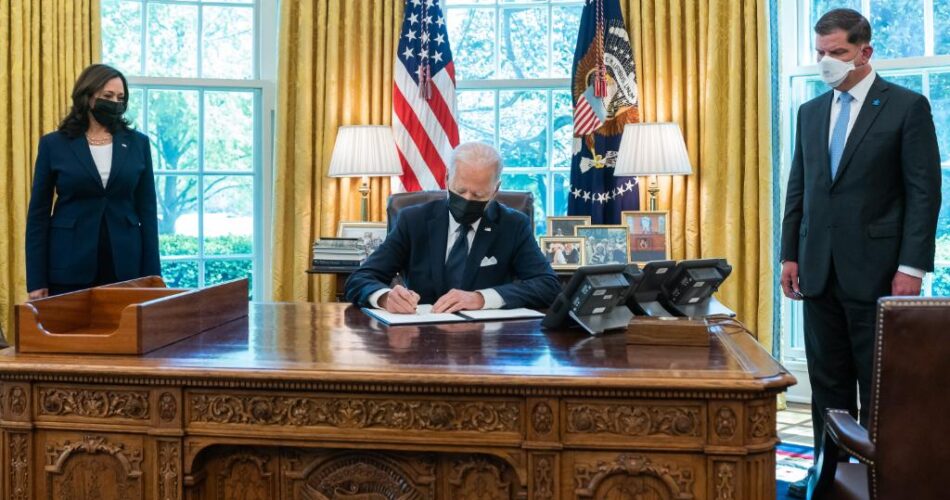
U.S. President Joe Biden today signed a national security memorandum that sets new cybersecurity requirements for National Security Systems run by the Department of Defense and the country’s intelligence agencies.
The order states that NSS requirements must meet or exceed the standard laid out for civilian federal agencies as detailed in an executive order signed by the President in May. That order, coming just after the attack on pipeline system operator Colonial Pipeline Co., included information sharing between the government and the private sector, mandating the use of multifactor authentication by government departments, establishing a Cybersecurity Safety Review Board and creating a standardized response playbook for responding to cyberattacks.
The new order authorizes the National Security Agency to issue binding operational directives to force agencies to “take specific actions against known or suspected cybersecurity threats and vulnerabilities.” The Department of Homeland Security has identical powers relating to civilian agencies under the previous May order.
A lot of the order goes into technicalities, but notable among the requirements is that every department or agency that operates an NSS must update its plans regarding cloud technology within two months. NSS agencies have also been given 180 days to implement MFA and encryption for NSS data-at-rest and data-in-transit.
All NSS agencies are also required to report any cybersecurity incidents that involve them to the NSA. The White House said that this reporting would help the government identify and mitigate cybersecurity risk across NSS.
“Agencies being required to identify their national security systems and report cyber incidents that involve them to the NSA aligns with the advice that industry often tells customers,” Mark Manglicmot, vice president of security services at security operations company Arctic Wolf Networks Inc., told SiliconANGLE. “To defend something, you need to have an asset inventory to know what your most critical systems and data are. This directive mandates this best practice.”
Manglicmot notes that new security standards and testing requirements for security tools are key. “Having a well-known standard sets a baseline that can be enforced and improved upon,” Manglicmot explained. “Testing is part of a mature security program to test its effectiveness and technical controls. Without testing, it’s unclear just how effective the implementation of these controls is – much less how to improve it as the threat landscape evolves.”
Tim Erlin, vice president of strategy at cybersecurity and compliance solutions firm Tripwire Inc., said the memorandum touches on many aspects of the original executive order, including promoting zero-trust architecture, implementing encryption and improving data sharing about incidents.
“It may be difficult for the average person to parse what’s happening here, but these kinds of artifacts, memorandums and executive orders, are key components in effectively operationalizing broadly applicable policy changes,” Erlin said. “For example, the inclusion of zero trust in this memorandum and in the executive order will cause agencies to make specific decisions about what technologies to purchase and implement.”
James McQuiggan, security awareness advocate at security awareness training company KnowBe4 Inc., said that one thing missing from the order is education around and the creation of a solid security culture among users. “When users can spot social engineering attacks, have the necessary training to work in Network or Security Operations Centers and understand the importance of developing secure code, it can strengthen the resiliency of the organization or government systems and significantly reduce the risk of a cyberattack,” McQuiggan added.
Photo: POTUS/Twitter
Show your support for our mission by joining our Cube Club and Cube Event Community of experts. Join the community that includes Amazon Web Services and Amazon.com CEO Andy Jassy, Dell Technologies founder and CEO Michael Dell, Intel CEO Pat Gelsinger and many more luminaries and experts.
Source link