A safety researcher disclosed on April 29, 2026, that Microsoft Edge decrypts each saved password into course of reminiscence the second the browser launches – and retains them there as cleartext for the whole session, no matter whether or not the consumer ever visits the websites these credentials belong to. The discovering, which has drawn vital consideration from safety professionals, places Edge’s credential dealing with in direct distinction with Google Chrome’s method and raises sensible issues for organizations operating shared Home windows environments.
The disclosure
The discovering was uncovered by researcher @L1v1ng0ffTh3L4N, who systematically examined each main Chromium-based browser for credential reminiscence dealing with conduct. In accordance with Cyber Safety Information, which reported on the disclosure, Edge was the one browser that exhibited this conduct – loading the whole password vault into plaintext course of reminiscence at startup and retaining it all through the session.
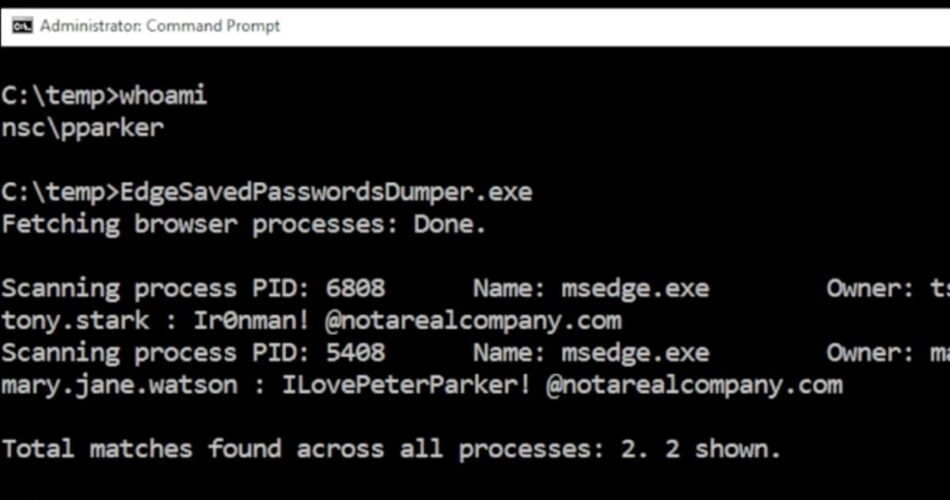
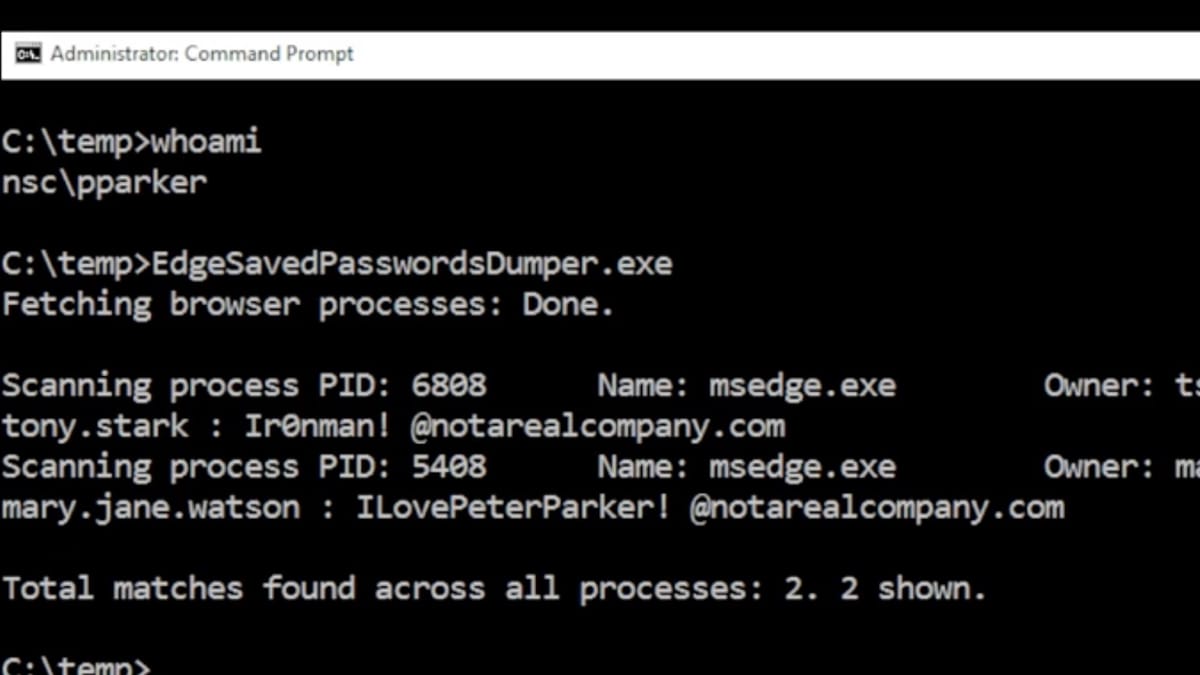
The disclosure occurred April 29 at BigBiteOfTech, offered by PaloAltoNtwks Norway alongside a small academic verification software. That software, launched publicly, permits any consumer to verify whether or not their Edge browser is holding cleartext credentials in course of reminiscence. On Could 4, 2026, researcher Tom Joran Sonstebyseter Ronning, recognized as @L1v1ng0ffTh3L4N on X, posted a video demonstration that gathered 5,900 replies and broad engagement inside hours.
When the researcher responsibly disclosed the discovering to Microsoft, the corporate’s official response was that the conduct is “by design.”
How Edge handles passwords in another way
The distinction with Google Chrome is technically vital. In accordance with Cyber Safety Information, Chrome implements on-demand decryption: credentials are decrypted solely in the mean time they’re wanted, particularly throughout autofill or when a consumer explicitly views a saved password. Chrome additional hardens its mannequin with App-Certain Encryption, which cryptographically binds decryption keys to an authenticated Chrome course of. This prevents different processes from reusing these keys to entry credentials.
Edge provides neither of those protections. From the second the browser opens, each saved credential throughout each web site within the consumer’s vault sits in plaintext within the browser’s course of reminiscence, making a persistent, wide-surface extraction goal for any attacker with the power to learn that course of reminiscence.
What makes the state of affairs significantly contradictory is Edge’s personal consumer interface conduct. In accordance with the disclosure, the browser nonetheless prompts customers for re-authentication earlier than revealing passwords within the Password Supervisor interface, but the identical browser course of already holds all these credentials in plaintext, fully accessible to anybody querying course of reminiscence. The re-authentication gate due to this fact offers solely the looks of entry management. It provides no safety in opposition to memory-based credential extraction.
App-Certain Encryption: what it does and doesn’t cowl
Within the LinkedIn dialogue that adopted the disclosure, Angus Holliday, a Senior Safety Operations Specialist, clarified the scope of Microsoft’s personal App-Certain Encryption coverage: “App-bound encryption protects at relaxation / key utilization. Does NOT shield reminiscence.” His remark underlines the hole: even the place App-Certain Encryption is enabled in Edge, it secures the encryption keys for knowledge saved on disk, not the plaintext credentials which are loaded into reminiscence at launch.
Microsoft’s coverage documentation for ApplicationBoundEncryptionEnabled, final up to date January 27, 2026, describes this function as binding “the encryption keys used for native knowledge storage to Microsoft Edge each time attainable.” The coverage web page notes that disabling it “has a detrimental impact on Microsoft Edge’s safety as a result of unknown and probably hostile apps can retrieve the encryption keys used to safe knowledge.” The coverage is supported on Home windows for Edge model 127 and above, and isn’t out there on macOS, Android, or iOS.
The important distinction, then, is between knowledge at relaxation and knowledge in reminiscence. App-Certain Encryption addresses the previous. The disclosure issues the latter – and Microsoft’s personal documentation acknowledges this hole. In accordance with Microsoft’s public steering on Edge password supervisor safety, “bodily native assaults and malware are outdoors the risk mannequin,” and “below these situations, encrypted knowledge could be weak.” The identical documentation states that if a pc is contaminated with malware, an attacker can get decrypted entry to the browser’s storage areas.
Reminiscence scraping as an assault vector
The severity of this discovering escalates considerably in shared or multi-user environments. In accordance with Cyber Safety Information, terminal servers and Distant Desktop Providers (RDS) installations are significantly uncovered. An attacker with administrative privileges on such a system can learn the reminiscence of each logged-on consumer course of concurrently. A printed proof-of-concept video accompanying the disclosure demonstrated a compromised administrator account efficiently extracting saved credentials from two different logged-on customers – together with customers with disconnected however nonetheless lively periods – by studying their Edge browser course of reminiscence.
This transforms a single admin-level compromise right into a full credential harvest throughout a whole multi-user surroundings. Cyber Safety Information notes the conduct maps on to MITRE ATT&CK T1555.003, the method classification for Credentials from Internet Browsers.
Within the LinkedIn dialogue, Anthony Godin, a Senior Programs Engineer at iQuest, noticed: “By Design is lacking the Safe half on the entrance, the half that’s meant to guide every thing first however is simply too typically an afterthought and by then hits the ‘too laborious’ basket.” One other commenter, Jamieson O’Reilly, founder at Dvuln.Hacker, famous that one of these vulnerability had been mentioned within the safety group for over a decade, including: “Google does a very good job at defending one of these knowledge due to the pressures they’ve needed to evolve in opposition to with infostealer malware.”
Microsoft’s said place
Microsoft’s present public documentation on Edge password supervisor safety acknowledges that in-memory credentials could be accessed below native assault situations and categorizes such eventualities as outdoors the browser’s risk mannequin. In accordance with that documentation, “Web browsers (together with Microsoft Edge) aren’t geared up with defenses to guard in opposition to threats the place the whole system is compromised as a result of malware operating because the consumer on the pc.”
The documentation additional acknowledges a structural actuality that applies to all browser password managers: “When browser passwords are encrypted on disk, the encryption secret is out there to any course of in your system, which incorporates any regionally operating malware. Even when passwords are encrypted in a ‘vault’ by a grasp key, they will be decrypted when loaded within the browser’s reminiscence area and could be harvested after you unlock the vault.”
What distinguishes the Edge discovering is just not that credentials exist in reminiscence sooner or later – that’s unavoidable for any browser that helps autofill – however that Edge masses the whole vault into plaintext at launch and holds it there constantly. Chrome limits the publicity window to the second credentials are literally used.
Microsoft’s documentation additionally confirms how the encryption mannequin works on the storage layer. In accordance with the Edge password supervisor safety steering, passwords are encrypted on disk utilizing AES, with the encryption key saved in an working system storage space. On Home windows, that storage space is DPAPI (Knowledge Safety API). On Mac, it’s the Keychain. The doc describes this method as native knowledge encryption. All these storage areas encrypt the AES key utilizing a key accessible to some or all processes operating because the consumer – a design alternative the doc explicitly notes “is commonly featured in blogs as a attainable exploit or vulnerability, which is an incorrect understanding of the browser risk mannequin.”
The enterprise implications
For organizations which have standardized on Microsoft Edge – a standard configuration in Home windows-centric enterprise environments – the disclosure raises sensible questions on terminal server deployments, VDI environments, and any shared-access techniques. Mike Pedrick, a CISO and GRC Chief who commented on the LinkedIn dialogue, obtained a reply noting: “At my final job Edge was the one browser allowed, every thing else was blocked – even Safari on the Macs. They stated it was for standardization and safety, however the reality was the CIO simply most well-liked it.”
That situation – Edge as the one permitted browser – is just not unusual. Safety groups in such environments now face a configuration threat that Microsoft has explicitly framed as intentional conduct fairly than a vulnerability requiring a patch.
Cyber Safety Information advisable that safety groups managing Home windows environments with Edge deployed, significantly these working terminal servers, VDI environments, or shared-access techniques, ought to deal with this as a high-priority configuration threat and think about migrating to browsers with on-demand decryption and App-Certain Encryption till Microsoft addresses the design determination.
The browser market context issues right here. In accordance with Cloudflare knowledge coated by PPC Land, Edge held 7.018% of the worldwide browser market in Q1 2025, putting it third behind Chrome at 63.409% and Safari at 17.496%. In enterprise environments, nonetheless, Edge’s share is significantly increased – significantly in organizations operating Microsoft 365 ecosystems the place Edge is the default browser on managed Home windows units.
The advertising and promoting trade is especially affected. As PPC Land reported in April 2026, browser-level knowledge dealing with has grow to be a serious point of interest, with analysis displaying over 80 Chrome extensions legally promoting shopping knowledge belonging to six.5 million customers. Advert tech corporations, companies, and advertising platforms routinely entry SaaS credentials, consumer marketing campaign techniques, and analytics dashboards by browsers on company units. A browser that holds each saved password in plaintext reminiscence from the second it launches represents a significant assault floor in that context.
The timing of the disclosure additionally follows a interval of heightened consideration to browser privateness structure. PPC Land previously covered Chrome’s transition to Manifest V3, which reshaped the extension ecosystem and sparked vital migration discussions. Extra broadly, browser safety selections now sit on the heart of enterprise safety posture in ways in which have been much less seen a number of years in the past.
What the coverage documentation says about suggestions
Microsoft’s personal password supervisor safety documentation takes a nuanced place on whether or not organizations ought to use the built-in Edge password supervisor. The doc lists a set of questions enterprise safety groups ought to think about, together with the type of attackers they’re fearful about, whether or not customers choose robust and distinctive passwords, whether or not accounts are protected with two-factor authentication, and the way units are shielded from malware.
The Microsoft safety staff eliminated its prior advice to disable the built-in password supervisor in Edge model 114, shifting that setting to “Not Configured” based mostly on the provision of recent options that altered the safety tradeoffs. In accordance with the documentation, “For many risk fashions, utilizing the Microsoft Edge password supervisor is the advisable choice.” That steering predates the April 2026 cleartext reminiscence disclosure, which particularly issues not whether or not to make use of the password supervisor however how Edge handles the credentials as soon as they’re saved.
The documentation additionally addresses the comparability with third-party password managers. It acknowledges that some third-party merchandise require a Grasp Password not saved regionally to decrypt credentials – providing partial mitigation in opposition to reminiscence scraping. Edge doesn’t at the moment provide this functionality, although the documentation notes that Microsoft provides an non-compulsory authentication-before-autofill function that “offers customers an extra layer of privateness and prevents their saved passwords from being utilized by anybody however them.”
No up to date steering from Microsoft had been printed in response to the April 29 disclosure as of the time of writing.
Timeline
- July 18, 2024: Microsoft publishes its Edge password supervisor safety documentation, final up to date on that date, acknowledging that credentials in reminiscence could be accessed below native assault situations and classifying such eventualities as outdoors the browser risk mannequin.
- January 27, 2026: Microsoft updates the ApplicationBoundEncryptionEnabled coverage documentation, masking Edge model 127 and above on Home windows, clarifying that the coverage binds encryption keys for native knowledge storage however doesn’t deal with in-memory credential storage.
- April 29, 2026: Researcher @L1v1ng0ffTh3L4N discloses the discovering at BigBiteOfTech, offered by PaloAltoNtwks Norway. The disclosure features a proof-of-concept video and a small academic verification software. Microsoft’s official response to the accountable disclosure: “by design.”
- Could 4, 2026: @L1v1ng0ffTh3L4N posts the proof-of-concept video on X, attracting 5,900 replies. Garett Moreau posts a abstract on LinkedIn describing the discovering to an expert viewers, producing 31 feedback and 42 reposts. Cyber Safety Information publishes an in depth writeup of the disclosure.
- Could 4, 2026: PPC Land covers LayerX research displaying over 80 Chrome extensions legally promoting shopping knowledge belonging to six.5 million customers, highlighting the broader context of browser-level knowledge publicity dealing with enterprise advertising and advert tech groups.
Associated PPC Land protection
Abstract
Who: Researcher @L1v1ng0ffTh3L4N, working below PaloAltoNtwks Norway, made the disclosure. Microsoft is the corporate whose browser conduct is described. Safety professionals commenting on LinkedIn embrace Angus Holliday, Anthony Godin, Jamieson O’Reilly, and Mike Pedrick.
What: Microsoft Edge decrypts each saved password into cleartext course of reminiscence in the mean time the browser launches and retains these credentials in plaintext for the whole browser session. Google Chrome, in contrast, makes use of on-demand decryption and App-Certain Encryption to restrict credential publicity. Microsoft has described the conduct as intentional.
When: The discovering was disclosed on April 29, 2026, at BigBiteOfTech. The proof-of-concept video and broader skilled dialogue emerged on Could 4, 2026. Microsoft’s official response – “by design” – was given in the course of the accountable disclosure course of previous to April 29.
The place: The vulnerability impacts Microsoft Edge operating on Home windows. Terminal servers, Distant Desktop Providers environments, VDI deployments, and any shared-access Home windows techniques are recognized because the highest-risk configurations. The disclosure was made on the BigBiteOfTech occasion, with the academic verification software launched publicly.
Why: The discovering issues as a result of it removes what customers may assume is a significant safety layer – the re-authentication immediate in Edge’s Password Supervisor UI – from the precise safety mannequin. Each saved credential is already accessible in plaintext course of reminiscence earlier than any UI interplay happens. In multi-user environments, a single admin-level compromise turns into a mechanism for harvesting credentials from each lively consumer session operating Edge. Microsoft has not printed up to date steering in response to the disclosure.
Share this text