Cyber correspondent
 Getty Pictures
Getty PicturesHackers regarded as working for the North Korean regime have efficiently cashed out not less than $300m (£232m) of their record-breaking $1.5bn crypto heist.
The criminals, referred to as Lazarus Group, swiped the large haul of digital tokens in a hack on crypto change ByBit two weeks ago.
Since then, it has been a cat-and-mouse sport to trace and block the hackers from efficiently changing the crypto into usable money.
Consultants say the notorious hacking crew is working practically 24 hours a day – doubtlessly funnelling the cash into the regime’s army improvement.
“Each minute issues for the hackers who’re making an attempt to confuse the cash path and they’re extraordinarily subtle in what they’re doing,” says Dr Tom Robinson, co-founder of crypto investigators Elliptic.
Out of all of the prison actors concerned in crypto forex, North Korea is the very best at laundering crypto, Dr Robinson says.
“I think about they’ve a whole room of individuals doing this utilizing automated instruments and years of expertise. We will additionally see from their exercise that they solely take just a few hours break every day, presumably working in shifts to get the crypto become money.”
Elliptic’s evaluation tallies with ByBit, which says that 20% of the funds have now “gone darkish”, which means it’s unlikely to ever be recovered.
The US and allies accuse the North Koreans of finishing up dozens of hacks lately to fund the regime’s army and nuclear improvement.
On 21 February the criminals hacked one in every of ByBit’s suppliers to secretly alter the digital pockets tackle that 401,000 Ethereum crypto cash had been being despatched to.
ByBit thought it was transferring the funds to its personal digital pockets, however as a substitute despatched all of it to the hackers.
 Getty Pictures
Getty PicturesBen Zhou, the CEO of ByBit, assured clients that none of their funds had been taken.
The agency has since replenished the stolen cash with loans from traders, however is in Zhou’s phrases “waging warfare on Lazarus”.
ByBit’s Lazarus Bounty programme is encouraging members of the general public to hint the stolen funds and get them frozen the place doable.
All crypto transactions are displayed on a public blockchain, so it is doable to trace the cash because it’s moved round by the Lazarus Group.
If the hackers attempt to use a mainstream crypto service to try to show the cash into regular cash like {dollars}, the crypto cash could be frozen by the corporate in the event that they assume they’re linked to crime.
Up to now 20 folks have shared greater than $4m in rewards for efficiently figuring out $40m of the stolen cash and alerting crypto corporations to dam transfers.
However specialists are downbeat concerning the probabilities of the remainder of the funds being recoverable, given the North Korean experience in hacking and laundering the cash.
“North Korea is a really closed system and closed financial system in order that they created a profitable trade for hacking and laundering they usually do not care concerning the detrimental impression of cyber crime,” Dr Dorit Dor from cyber safety firm Test Level stated.
One other downside is that not all crypto firms are as keen to assist as others.
Crypto change eXch is being accused by ByBit and others of not stopping the criminals cashing out.
Greater than $90m has been efficiently funnelled via this change.
However over e-mail the elusive proprietor of eXch – Johann Roberts – disputed that.
He admits they did not initially cease the funds, as his firm is in a long-running dispute with ByBit, and he says his crew wasn’t certain the cash had been undoubtedly from the hack.
He says he’s now co-operating, however argues that mainstream firms that establish crypto clients are abandoning the personal and nameless advantages of crypto forex.
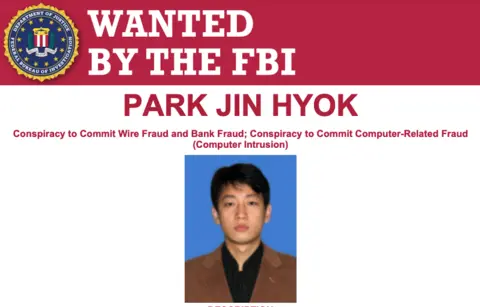 FBI
FBINorth Korea has by no means admitted being behind the Lazarus Group, however is regarded as the one nation on this planet utilizing its hacking powers for monetary acquire.
Beforehand the Lazarus Group hackers focused banks, however have within the final 5 years specialised in attacking cryptocurrency firms.
The trade is much less properly protected with fewer mechanisms in place to cease them laundering the funds.
Current hacks linked to North Korea embody:
- The 2019 hack on UpBit for $41m
- The $275m theft of crypto from change KuCoin (many of the funds had been recovered)
- The 2022 Ronin Bridge assault which noticed hackers make off with $600m in crypto
- Roughly $100m in crypto was stolen in an assault on Atomic Pockets in 2023
In 2020, the US added North Koreans accused of being a part of the Lazarus Group to its Cyber Most Needed listing. However the probabilities of the people ever being arrested are extraordinarily slim until they depart their nation.
Source link




